Will quantum computers be able to decrypt data?
It doesn’t take much for quantum computers to solve issues that would confound even the most powerful supercomputer for hours. It’s true that these issues are theoretically far from being solved, and that quantum systems have significant limitations. We can’t stop the march of time, and this technology has the potential to rule the globe someday. Take a look at how that impacts your information below.
An important part of Internet security is data encryption.
When it comes to keeping sensitive information safe on computers and the internet, encryption is king. The goal of encryption is to change the information being sent into an incomprehensible string of characters using a predetermined set of algorithms as well as a character collection called as a key. The gibberish must be decoded, also using a key, to learn what the sender intended to convey.
A cipher is considered to be symmetric if it only requires one key to decipher it, and that key is known to both parties. In order to start exchanging communications, everyone must have the key to encrypt and decode messages. Furthermore, the key must be sent without encryption. Moreover, if this takes place online, malicious actors may be able to access and view the purportedly private communications. It’s not looking good.
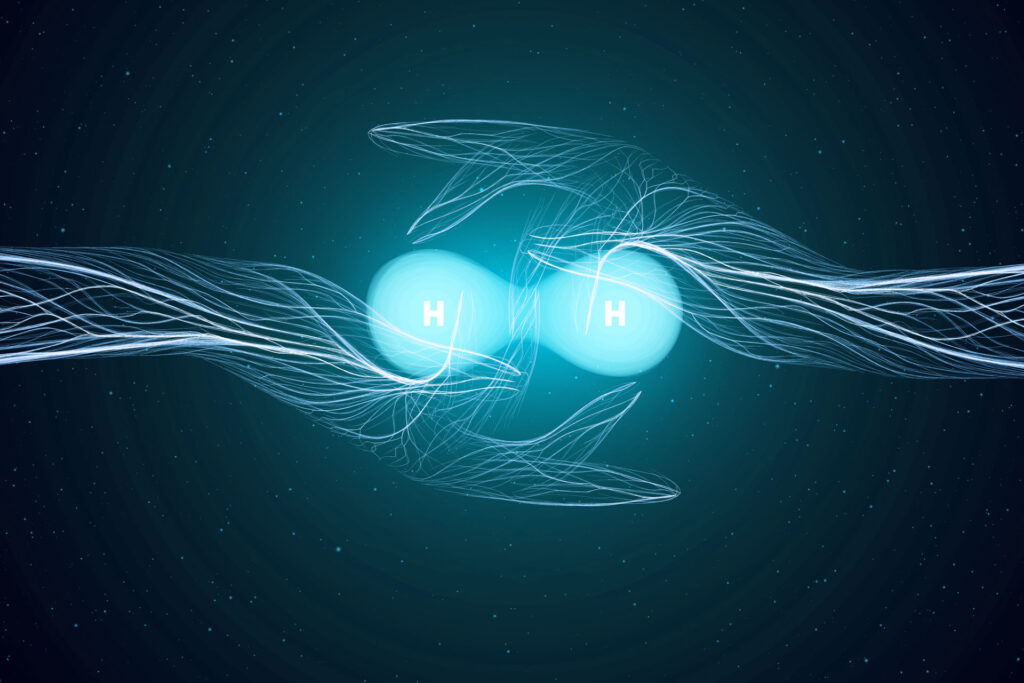
Certain algorithms which encode data employ pair of keys, one of which is kept secret and is used to decode data, while the other is made public and is used to encrypt data. Both are made by the lucky receiver. It is impossible to acquire the private key since it is never revealed to anybody.
While anybody may use the secondary, public key to encrypt data, only those in possession of the accompanying private key will be able to decode it. That’s why it’s perfectly safe to email the public key in plaintext or publish it online where anybody may view it. Asymmetric cryptography describes this kind of protection.
Keys in current encryption systems are often extremely big numbers, and also the algorithms actually are typically based on sophisticated mathematical calculations with these numbers. In addition, the procedures are designed in such a way that undoing them would be very difficult. Therefore, it is useless to have the public key in an attempt to decipher the encryption.
Quantum encryption breaking
But there’s a caveat. In a strict sense, encryption techniques are built such that breaking the cipher takes an unreasonably long period of time. This is when quantum computers come into play. They are much quicker at number crunching than desktop computers. Therefore, on a quantum computer, the amount of time required to break the encryption that would be ridiculous on a conventional computer may be completely acceptable. And if a cipher can be broken using quantum computing, then defeats the purpose of adopting encryption in the first place.
Defense against Quantum-Cracking Attempts
If the prospect of well-funded thieves using a quantum computer to decipher and steal your data gives you the willies, take heart: information security professionals are already hard at work finding solutions. There are now a number of simple safeguards in place to prevent unauthorized access to sensitive user data.
Protected against quantum assaults using time-tested methods of encryption. While it’s difficult to believe, we’re already employing encryption technologies that are secure against quantum computers. For instance, the widely-used AES method, which is used by IM services like WhatsApp and Signal, is an excessively difficult nut to crack, despite the fact that quantum computers hasten the procedure, although little. While the access control issue noted above remains, these attacks are not fatal to numerous other symmetric ciphers (those that use just one key).
Security algorithms designed to withstand quantum assaults.
Mathematicians are already working on new forms of encryption that will be impenetrable by even the most advanced quantum computers. Although data security systems may not be ready to counteract quantum computers immediately, they will likely be ready by the time hackers develop and use such powerful weapons.
Multiple-method simultaneous encryption.
Using several encryption techniques on the same data is a good option that’s accessible currently. It is quite improbable that attackers will be able to break through all of them, even if they manage to breach one.
The inversion of quantum technology.
In particular, quantum key distribution systems may improve the security of symmetric ciphers, which are less susceptible to quantum breaking. While this doesn’t ensure security against hackers, at least you’ll know if your data was collected and may resend the encryption key if it gets stolen. Yes, specialized machinery is needed for that, but the good news is that there is already working machinery of this kind in use by various public and private sectors.
That’s not the end of cyber safety
Quantum computers may be able to decipher codes that are inaccessible to classical computers, but they are far from perfect. Cybersecurity solutions are also evolving ahead of the game, meaning they won’t give adversaries any ground in the ongoing arms race.
Certain encryption algorithms may likely become more popular and replace others over time, which is not a negative thing for the field of cryptography as a whole. As we’ve indicated, progress is never static, therefore it’s occurring right now.
In light of this, it is prudent to periodically verify which encryption technique a service employs and whether or not it is no longer secure. For very significant material that will be stored for a long time, it is prudent to encrypt it as though the age of quantum computers has already arrived.
Image by Gerd Altmann from Pixabay